Quantum Security: What’s Real, What’s Hype, and What’s Actionable Today
The quantum threat to cryptography is approaching - but the most pressing opportunities are already here.
33N backed founders and team at a dinner last week in RSA.
TL;DR:
Quantum computing remains years away from practical advantage, but the cryptographic threat it poses is already here.
“Harvest now, decrypt later” attacks - where adversaries collect encrypted data today to crack it once quantum hardware matures - are a live concern for any organisation holding sensitive long-lived data. In response, regulatory deadlines are tightening across the world.
Crypto agility, the ability to discover, inventory, and swap cryptographic assets rapidly, is an essential need to prepare for the coming changes in paradigm.
At 33N, we’ve been spending time mapping the quantum landscape - not just the physics, but where it intersects with cybersecurity. It’s a space full of bold claims and uncertain timelines, so we wanted to share what we’ve found: what the real state of maturity is, what the threat actually looks like, and where enterprises and investors should focus today.
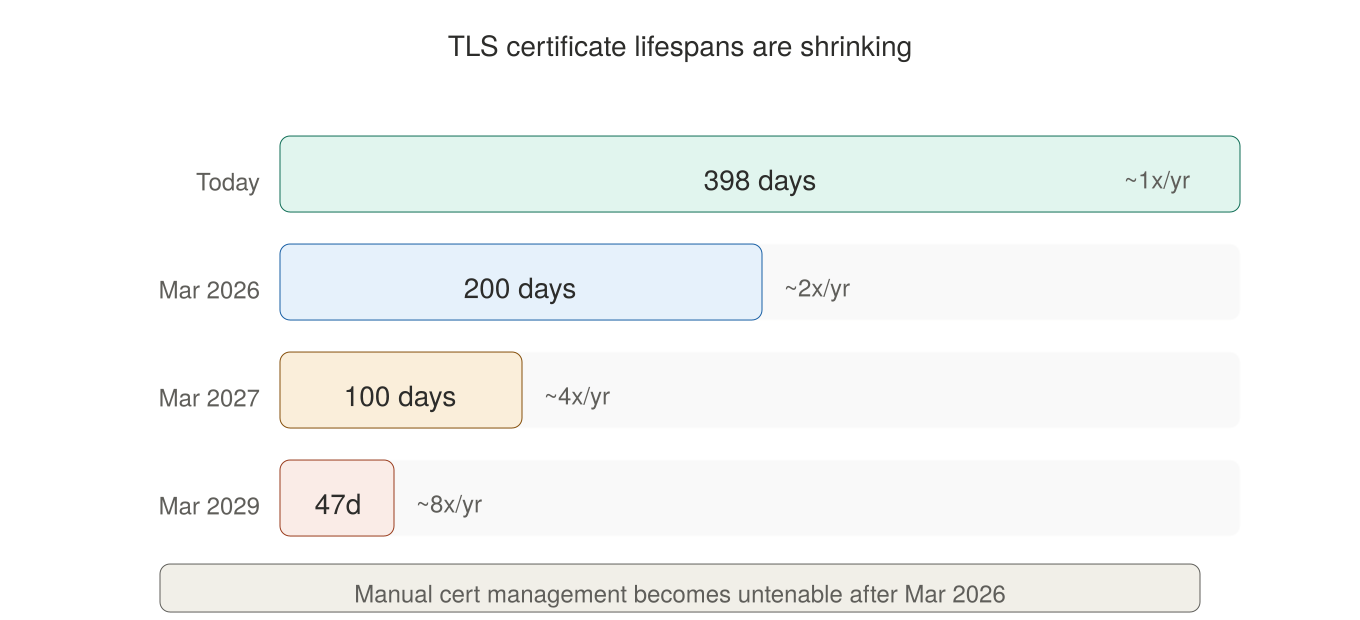
TLS certificate lifespans dropped from 398 days to 200 and will gradually reduce to 47 days by 2029 [18]. Cloudflare became the first SASE platform to ship post-quantum encryption across its entire stack — pushed automatically to customers, no configuration required [19]. D-Wave closed a $550M acquisition of Quantum Circuits to bring error-corrected quantum systems to market [20]. And Microsoft is preparing to deliver its first error-corrected quantum computers to customers this year [21].
The quantum era isn’t here yet — but the infrastructure shift it demands has already begun.
Quantum Computing - Where Are We Really?
Quantum computing is a fundamentally different way of processing information. Instead of classical bits (0 or 1), quantum computers use qubits that can exist in superposition - representing multiple states simultaneously - and leverage entanglement to create computational methods with no classical equivalent. But quantum computers are not simply faster supercomputers. They offer speedups only for specific classes of problems - cryptography, quantum simulations of molecules and materials, and certain optimization tasks. For everyday computing, classical machines remain superior. The industry is increasingly moving toward specialized quantum hardware designed for narrow problem sets rather than general-purpose machines. [1]
In practice, the technology is still gated by hardware maturity. Useful quantum computing depends on scaling up qubit counts, extending coherence times (how long qubits maintain their quantum state), and - critically - achieving reliable error correction.
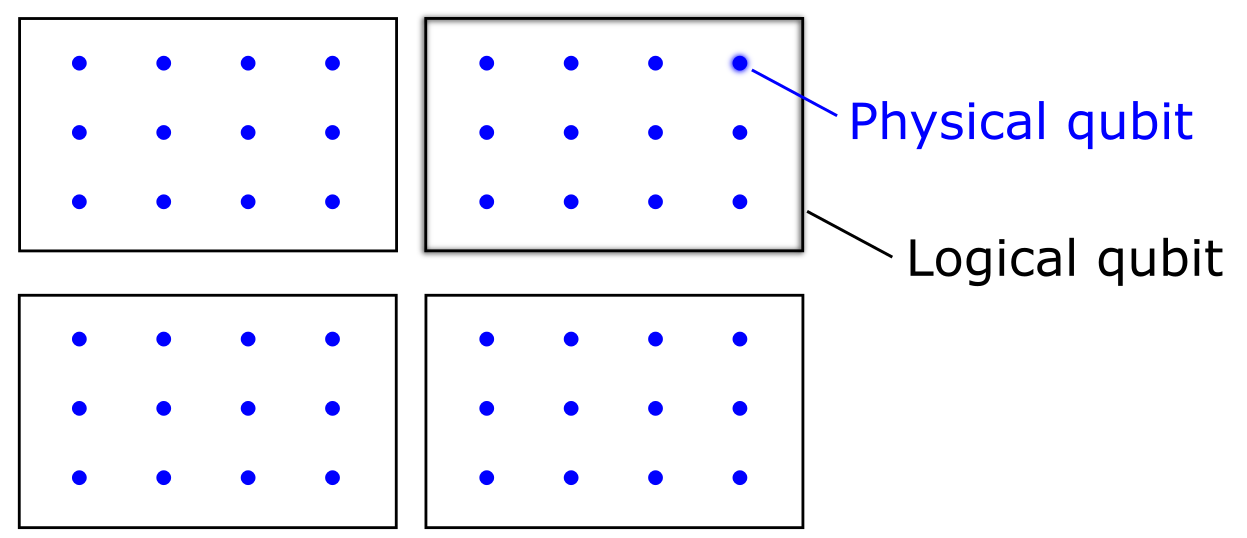
One recent push has been the shift towards abstraction from focusing on physical qubits to logical qubits (groupings of logical qubits) to address these issues. [1]
Figure 1: Distinction Physical and Logical Qubits (Intro to Quantum)
Still, current quantum systems fit the called NISQ (Noisy Intermediate-Scale Quantum computer) class, meaning they are noisy, fragile, and limited in scope.
What exists today are mostly hybrid approaches: classical computers handle the bulk of processing and call on quantum hardware for specific subproblems. This has led to early demand for orchestration and scheduling software to manage these hybrid workflows, though the real-world adoption of these tools remains nascent. [24]
Most roadmaps suggest that practical quantum advantage - quantum computers consistently outperforming classical ones on useful tasks - is still five to fifteen years away, with wide disagreement on timelines. [2]
The quantum computing market is estimated at roughly $1–3.5 billion in 2025, with projections varying from $4 billion to $20 billion by 2030 depending on the source - reflecting genuine uncertainty about how quickly the technology will commercialize. [3] [4] [5]
A recent paper in Science described quantum technology as having reached “equivalent of the early transistor age” — functional systems exist, but scaling them requires major engineering breakthroughs [23]. Microsoft (in collaboration with Atom Computing) plans to deliver an error-corrected machine to research partners in Denmark, while QuEra plans to make error-corrected systems available to global customers — both targeting 2026 [20][21].
But as QuEra’s own chief commercial officer put it:
“If someone says quantum computers are commercially useful today, I say I want to have what they’re having.” [21]
It’s also worth noting that this is a space highly sensitive to headlines. When Jensen Huang commented at CES in January 2025 that practical quantum computers were “at least 15 years away,” quantum stocks plunged - Rigetti fell around 40%, IonQ dropped around 35%, and billions in combined market cap evaporated in a single day. [6] Two months later, Huang hosted a “Quantum Day” at Nvidia’s GTC conference to walk it back. [7]
The episode illustrates how much hype, rather than fundamentals, still drives the space.
The space of quantum computing and quantum related solutions is too vast for us to be able to cover every segment here but these are some companies that we came across while looking at the ecossystem: Qilimanjaro, Multiverse Computing, Alice & Bob, Entanglement, Quside, Wultra, Quantropi
If you are interested in learning more about Quantum Computing we strongly recommend the following article from V. Raseena.
The Quantum Threat to Cryptography
The clearest near-term impact of quantum computing isn’t about giving enterprises new computational power - it’s the threat to current encryption.
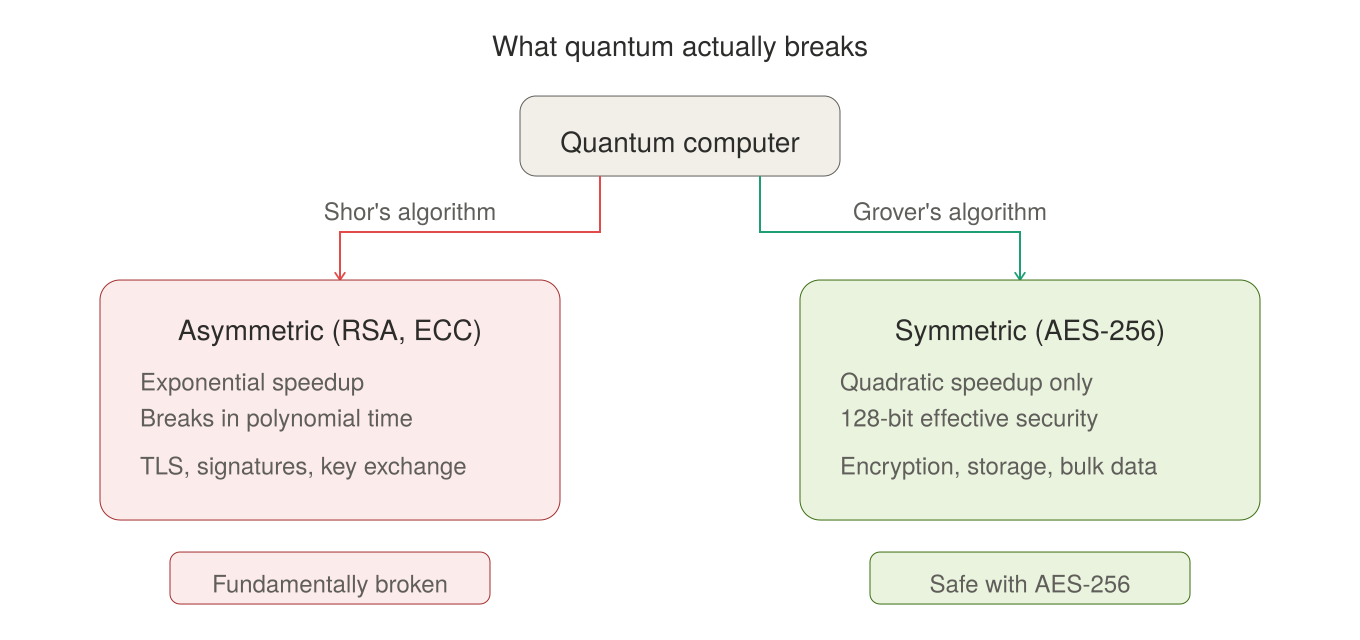
Most modern encryption depends on asymmetric cryptography (RSA, ECC), which is built on mathematical problems that are extremely hard for classical computers to solve.
Quantum computers, once mature enough, could break these in polynomial time using algorithms like Shor’s. [25]
Symmetric encryption (such as AES) is far less vulnerable - Grover’s algorithm only provides a quadratic speedup, meaning larger key sizes are sufficient to maintain security. [26] [29]
The real threat is to asymmetric cryptography. [27] [12]
Figure 2: Quantum computing primarily threatens asymmetric encryption.
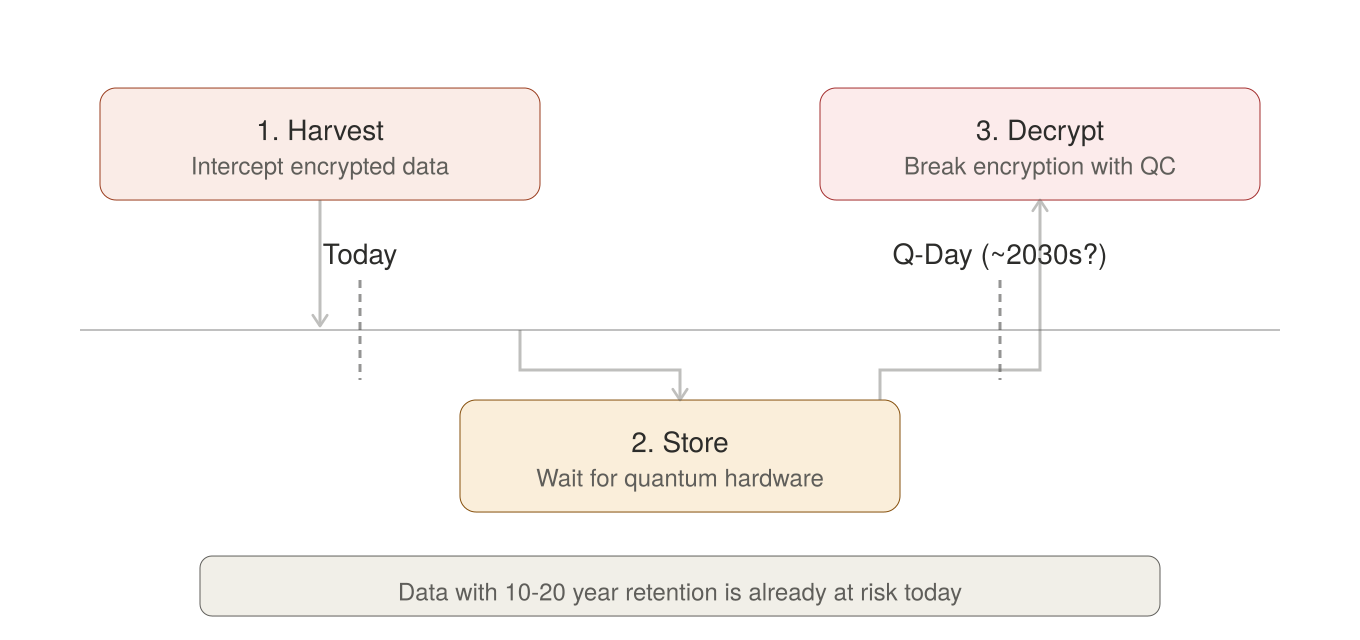
But here’s the critical insight: you don’t need quantum computers to exist yet for the threat to be real and already relevant.
In what’s known as a “harvest now, decrypt later” attack, adversaries intercept and store encrypted data today, waiting until quantum hardware matures enough to crack it.
For any data with long retention requirements - government records, financial transactions, health data, intellectual property - this is a live concern right now. [30][31]
A 2025 industry survey found that 60% of organizations are already very concern about these tactics. [8] With NIST seeing this as threat that justifies immediate migration and making the following joint recommendation alongside NSA and CISA:
“A successful post-quantum cryptography migration will take time to plan and conduct. CISA, NSA, and NIST urge organizations to begin preparing now by creating quantum-readiness roadmaps, conducting inventories, applying risk assessments and analysis, and engaging vendors. Early planning is necessary as cyber threat actors could be targeting data today that would still require protection in the future (or in other words, has a long secrecy lifetime), using a catch now, break later or harvest now, decrypt later operation.” [33][34]
Figure 3: The harvest now, decrypt later threat - data stolen today can be decrypted once quantum hardware matures.
Regulatory bodies have taken notice. NIST published its first post-quantum cryptography standards in August 2024. [9] In the US, federal agencies must support TLS 1.3 by January 2030, national security systems must be fully CNSA 2.0 compliant by 2031, and NIST plans to deprecate and disallow quantum-vulnerable algorithms entirely by 2035. [10] [11] [12] Australia targets 2030 for eliminating classical public-key cryptography. [13] The EU’s coordinated roadmap targets 2030 for high-risk systems and 2035 for broader completion.
The direction is clear, and the migration timeline itself creates urgency regardless of when a cryptographically relevant quantum computer actually arrives.
Three Approaches to Quantum-Safe Cryptography
The industry is converging on three main approaches to quantum-safe cryptography, each with distinct trade-offs.
Post-Quantum Cryptography (PQC) refers to new encryption algorithms - that run on classical hardware and are designed to resist quantum attacks. NIST standardized the first set in August 2024 after an eight-year global review involving industry, academia, and governments. [9] They’re software-based and relatively cost-effective to deploy.
The catch: like all encryption, these algorithms cannot be mathematically proven secure - they represent the best candidates based on rigorous peer review, but they’re newer and less battle-tested than the algorithms they replace. They’re also prone to larger key-sizes which brings integration concerns and can impact performance in certain systems.
Quantum Key Distribution (QKD) takes a physics-based approach. Instead of relying on mathematical hardness, it uses quantum mechanics (specifically, the behavior of photons) to distribute encryption keys. Any attempt to intercept the key disturbs the quantum state and is detectable. In theory, it’s provably secure.
In practice, it’s expensive, requires dedicated fiber infrastructure, and fiber-QKD is range limited. Government agencies have been notably cautious: the US NSA explicitly does not support the use of QKD for national security communications, [14] the UK’s NCSC has stated it will not support QKD for government or military applications, [15] and a joint 2024 position paper by France’s ANSSI, Germany’s BSI, and agencies from the Netherlands and Sweden concluded that QKD is not yet sufficiently mature from a security perspective. [16]
That said, China is actively investing in QKD infrastructure - China has deployed a 10,000+ km QKD network - creating a real geopolitical split in approaches. [17][36]
Some solutions also incorporate pre-shared symmetric keys (PSK) for additional security layers - an approach endorsed by the NSA for classified systems through its Commercial Solutions for Classified (CSfC) program. Unlike PQC (math-based) or QKD (physics-based), symmetric key approaches rely on securely delivering shared random data out-of-band, which is logistically complex but can provide strong security guarantees when implemented correctly.
Authorities broadly recommend a hybrid combination for deploying PQC, using classical algorithms alongside it during the transition. [37]
The real question for most enterprises isn’t which algorithm to pick - it’s how to manage the transition.
A few players in these spaces: PQShield, KETS Quantum Security, SpeQtral, QuantumBridge, Arqit Group.
What’s Actionable Right Now - Crypto Agility
For all the uncertainty around quantum timelines, from our conversations with experts and market participants, crypto agility consistently surfaces as one of the most practical and immediate area of focus - both as a standalone capability and as the foundation for any future PQC migration.
Crypto agility is the ability of an organization to replace its existing cryptographic primitives, algorithms, or protocols with alternatives quickly and without business disruption.
It’s a concept that predates quantum concerns, but the risks posed by “harvest now, decrypt later” and impending Q-Day fears put this on top of the mind of security leaders.
Before an organization can migrate to quantum-safe algorithms, it needs to answer a deceptively simple question: what cryptography are we actually using, and where?
In practice, most enterprises don’t have this visibility. According to a 2025 industry report, only 28% of organizations maintain a full certificate inventory, and just 13% are confident they track all certificates - including rogue ones deployed outside official processes. [8] Without that visibility, any migration effort is flying blind.
This matters beyond quantum. Certificate lifespans are already shrinking fast. In April 2025, the CA/Browser Forum voted to reduce TLS certificate lifespans on a phased schedule: 200 days from March 2026, 100 days from March 2027, and 47 days from March 2029. [18]
This makes automated certificate lifecycle management an operational necessity - and crypto agility the foundation for handling both the quantum transition and the day-to-day reality of modern PKI.
Figure 4: TLS certificate lifespans are dropping to 47 days by 2029.
The migration path itself is non-trivial. Organizations will likely need to run classical and PQC in tandem, maintain backward compatibility during transition periods, and handle complexity across hardware, software, and network layers.
As Cloudflare’s own team noted, the lack of crypto agility — the ability to easily swap cryptographic algorithms — is the major bottleneck for most organizations [19]. MD5, broken in 2004 for the first time, is still used and thus a major vulnerability [38].
Despite progress at the client and transport layers [19], back-end systems — including origin infrastructure, certificate management, and legacy application dependencies — are still lagging.
This is where crypto agility becomes critical: it allows organizations to adapt cryptographic components with less operational disruption as the transition unfolds.
A few players in this space: QuSecure, Keyfactor, CryptoNext, ExeQuantum
The Takeaway
Quantum computing’s full potential is still years away, and timelines remain genuinely uncertain. Breakthroughs could accelerate the timeline dramatically, or persistent engineering challenges could push practical quantum advantage further out. Anyone claiming certainty is selling something.
But the cryptographic migration that quantum demands is already underway, driven by regulation, real threats like harvest-now-decrypt-later, and the operational pressures of modern certificate management.
Crypto agility is valuable regardless of when quantum arrives.
The quantum era may be uncertain, but the preparation for it is not.
If you’re building in quantum security or exploring the PQC transition, we’d love to exchange notes.
Reach out - and let the winds keep blowing.
33N Portfolio Updates 🚀
Acoru
Started their podcast Fraud Signals, watch here
Apono
Released its 2026 State of Agentic AI Cyber Risk Report, finding that 98% of cybersecurity leaders are slowing agentic AI adoption because security controls are not yet ready.
Launched Agent Privilege Guard, runtime guardrails to enterprise AI agents
DataGalaxy
Launched Portfolio, a new domain-driven governance framework designed to connect data strategy with business execution, helping enterprises run data and AI as a global value portfolio.
Equixly
Recognized as a top Scale-up in OVHcloud ecosystem awards.
Exein
Won the Award for Safety and Security in Embedded World 2026
Named top-3 cybersecurity startup in Sifted’s hottest sector to watch in 2026
Announced partnership with Abinsula and MeshSystem
Unveiled Photon, the kernel-level runtime security platform for industrial/AI systems
StrikeReady
Announced the integration with Netskope
Alex Lanstein, CTO, was featured in TechTarget’s article “From security to trust: How AI is tranforming the CISO’s Job”
Upcoming Events for 33N 🤝
FIC, Lille, 31 Mar–2 Apr
NCSC CyberUK, Glasgow, 21–23 Apr
GISEC, Dubai, 5-7 May
SIM Conference, Porto, 14-15 May
InfoSecurity Europe, London, 2-3 Jun.
South Summit, Madrid, 3-5 Jun.
Super Return Venture, Berlin, 9-10 Jun.


Sources
[1] Moody’s, “Quantum Computing’s Six Most Important Trends for 2025.” moodys.com/web/en/us/insights/quantum/quantum-computings-six-most-important-trends-for-2025.html
[2] Raseena V., “Quantum Computing: Foundations, Algorithms, and Emerging Applications.” Frontiers in Quantum Science and Technology, December 2025. doi.org/10.3389/frqst.2025.1723319
[3] Precedence Research, “Quantum Computing Market Size.” February 2026. Market valued at $1.44B in 2025. precedenceresearch.com/quantum-computing-market
[4] MarketsandMarkets, “Quantum Computing Market.” Market valued at $3.52B in 2025, projected $20.2B by 2030 (41.8% CAGR). marketsandmarkets.com/Market-Reports/quantum-computing-market-144888301.html
[5] Grand View Research, “Quantum Computing Market Size.” Market valued at $1.42B in 2024, projected $4.24B by 2030 (20.5% CAGR). grandviewresearch.com/industry-analysis/quantum-computing-market
[6] Fortune, “Nvidia CEO Jensen Huang Just Tanked Quantum-Computing Stocks.” January 2025. fortune.com/2025/01/09/nvidia-ceo-jensen-huang-tanks-quantum-computing-stocks/
[7] CNBC, “Nvidia CEO Jensen Huang Says He Was Wrong About Timeline for Quantum.” March 2025. cnbc.com/2025/03/20/nvidia-ceo-huang-says-was-wrong-about-timeline-for-quantum-computing.html
[8] Sectigo & Omdia, “The State of Crypto Agility 2025.” Survey of 272 IT decision-makers. sectigo.com/uploads/resources/Sectigo-State-of-Crypto-Agility-Report-2025.pdf
[9] NIST, “NIST Releases First 3 Finalized Post-Quantum Encryption Standards.” August 2024. nist.gov/news-events/news/2024/08/nist-releases-first-3-finalized-post-quantum-encryption-standards
[10] Executive Order 14144 / 14306, TLS 1.3 adoption required by January 2, 2030. Detailed analysis: postquantum.com/quantum-policies/us-pqc-regulatory-framework-2026/
[11] CNSSP 15 / CNSA 2.0: New NSS acquisitions compliant by Jan 2027; phase-out of non-compliant equipment by Dec 2030; full mandate by Dec 2031. paloaltonetworks.com/cyberpedia/pqc-standards
[12] NIST IR 8547 (draft), “Transition to Post-Quantum Cryptography Standards.” Deprecation by 2035. csrc.nist.gov/projects/post-quantum-cryptography
[13] Australian Signals Directorate (ASD), target to eliminate classical public-key cryptography by 2030. Referenced in Palo Alto Networks PQC Standards guide.
[14] NSA, “Quantum Key Distribution (QKD) and Quantum Cryptography (QC).” nsa.gov/Cybersecurity/Quantum-Key-Distribution-QKD-and-Quantum-Cryptography-QC/
[15] UK National Cyber Security Centre (NCSC), 2025 guidance on QKD. Referenced in postquantum.com/post-quantum/qkd-countries-differ/
[16] ANSSI, BSI, NLNCSA, Swedish Armed Forces, “Position Paper on Quantum Key Distribution.” 2024. bsi.bund.de/SharedDocs/Downloads/EN/BSI/Crypto/Quantum_Positionspapier.pdf
[17] RAND Corporation, “U.S.-Allied Militaries Must Prepare for the Quantum Threat to Cryptography.” June 2025. rand.org/pubs/commentary/2025/06/us-allied-militaries-must-prepare-for-the-quantum-threat.html
[18] DigiCert, “TLS Certificate Lifetimes Will Officially Reduce to 47 Days.” CA/Browser Forum ballot SC-081v3, passed April 2025. digicert.com/blog/tls-certificate-lifetimes-will-officially-reduce-to-47-days
[19] Cloudflare, "Cloudflare One is the first SASE offering modern post-quantum encryption across the full platform." Feb 2026. blog.cloudflare.com/post-quantum-sase/
[20] D-Wave, "D-Wave Announces Agreement to Acquire Quantum Circuits Inc." $550M transaction. ir.dwavequantum.com
[21] IEEE Spectrum, "Neutral Atom Quantum Computing: 2026's Big Leap." Feb 2026. spectrum.ieee.org/neutral-atom-quantum-computing
[22] Cloudflare, "State of the post-quantum Internet in 2025." Oct 2025. blog.cloudflare.com/pq-2025/
[23] Awschalom et al., "Challenges and Opportunities for Quantum Information Hardware." Science, 2025. doi.org/10.1126/science.adz8659
[24] U.S. Data Science Institute (USDSI), "Latest Developments in Quantum Computing: 2026 Edition." Jan. 2026. [Online]. Available: https://www.usdsi.org/data-science-insights/latest-developments-in-quantum-computing-2026-edition
[25] Shor, P.W., "Polynomial-Time Algorithms for Prime Factorization and Discrete Logarithms on a Quantum Computer." SIAM Journal on Computing, 26(5), 1484–1509, 1997. epubs.siam.org/doi/10.1137/S0036144598347011
[26] Grover, L.K., "A Fast Quantum Mechanical Algorithm for Database Search." Proceedings of the 28th Annual ACM Symposium on Theory of Computing (STOC '96), 212–219, 1996. arxiv.org/abs/quant-ph/9605043
[27] NIST, "Post-Quantum Cryptography: FIPS 203, 204, and 205." First three post-quantum cryptographic standards, finalized Aug. 13, 2024. csrc.nist.gov/news/2024/postquantum-cryptography-fips-approved
[29] Grassl, M. et al., "Applying Grover's Algorithm to AES: Quantum Resource Estimates." arXiv:1512.04965, 2015. Establishes qubit and gate counts for Grover-based key search on AES-128, -192, and -256. arxiv.org/abs/1512.04965
[30] Palo Alto Networks, "Harvest Now, Decrypt Later (HNDL): The Quantum-Era Threat." Cyberpedia explainer on HNDL attacks and post-quantum migration. paloaltonetworks.com/cyberpedia/harvest-now-decrypt-later-hndl
[31] Mascelli, Jillian, and Megan Rodden. "'Harvest Now Decrypt Later': Examining Post-Quantum Cryptography and the Data Privacy Risks for Distributed Ledger Networks." Finance and Economics Discussion Series 2025-093. Board of Governors of the Federal Reserve System, September 2025. doi.org/10.17016/FEDS.2025.093
[33] Palo Alto Networks. "What Is Q-Day, and How Far Away Is It — Really?" Cyberpedia. paloaltonetworks.com/cyberpedia/what-is-q-day
[34] CISA, NSA, and NIST. "Quantum-Readiness: Migration to Post-Quantum Cryptography." Joint Cybersecurity Factsheet. August 21, 2023. cisa.gov/resources-tools/resources/quantum-readiness-migration-post-quantum-cryptography
[35] European Commission / NIS Cooperation Group, "A Coordinated Implementation Roadmap for the Transition to Post-Quantum Cryptography." June 2025. digital-strategy.ec.europa.eu/en/library/coordinated-implementation-roadmap-transition-post-quantum-cryptography
[36] Chen, H-Z., Li, M-H., Wang, Y.Z. et al., "Implementation of Carrier-Grade Quantum Communication Networks over 10000 km." npj Quantum Information, vol. 11, article 137, August 2025. nature.com/articles/s41534-025-01089-8
[37] BSI, ANSSI, and agencies from 21 European states, "Joint Statement on the Transition to Post-Quantum Cryptography." 2025. bsi.bund.de/SharedDocs/Downloads/EN/BSI/Crypto/PQC-joint-statement-2025.pdf
[38] Cloudflare, "RADIUS/UDP vulnerable to improved MD5 collision attack." July 2024. blog.cloudflare.com/radius-udp-vulnerable-md5-attack